Prepare for more frequent BIND security updates
Plan for more frequent BIND security updates, at least for the remainder of 2026.
ReadVersatile, classic, complete name server software
BIND 9 has evolved to be a very flexible, full-featured DNS system. Whatever your application is, BIND 9 probably has the required features. As the first, oldest, and most commonly deployed solution, there are more network engineers who are already familiar with BIND 9 than with any other system.
BIND 9 is transparent open source, licensed under the MPL 2.0 license. Users are free to add functionality to BIND 9 and contribute back to the community through our open Gitlab.
If you want source code, download a current version from the ISC website or our FTP site. Or, install our updated ISC packages for Ubuntu, CentOS/Fedora, and the standard Debian package. If you prefer Docker, get our official Docker image.
Help is available via our community mailing list, or you may purchase a support subscription for expert, confidential, 24×7 support from the ISC team.
Contact ISC for Support
Before your mail server sends an email, before your web browser displays a web page, there is a DNS lookup to resolve a DNS name to an IP address. Watch this DNS Fundamentals presentation from Eddy Winstead of ISC or read A Warm Welcome to DNS by Bert Hubert of PowerDNS. You may also enjoy this blog post from Jeff Osborn of ISC about how the Root Server System operates.
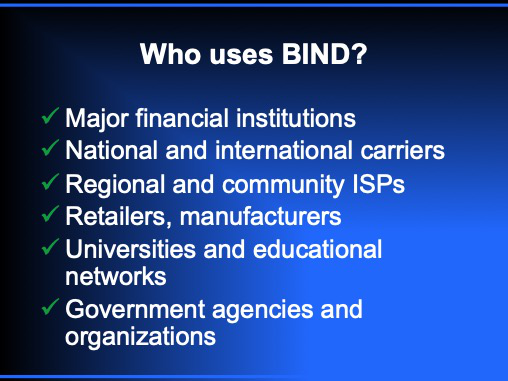
BIND is used successfully for every application from publishing the (DNSSEC-signed) DNS root zone and many top-level domains, to hosting providers who publish very large zone files with many small zones, to enterprises with both internal (private) and external zones, to service providers with large resolver farms.
We support three major branches of BIND 9 at a time: Stable, Extended-Support, and Development. See this advice: Which version of BIND do I want to download and install? as well as our list of supported platforms.
We also maintain a significant feature matrix and changes file. When upgrading to a newer version, we recommend reviewing significant changes such as this article on Changes to be aware of when moving from BIND 9.18 to 9.20.
If you would prefer a GUI management interface, you might consider a Commercial Product based on BIND.
Instructions are available for Installing and Upgrading the latest version of BIND 9. ISC provides packages for Ubuntu and CentOS EPEL and Fedora and Debian - BIND 9 ESV, Debian - BIND 9 Stable, Debian - BIND 9 Development version. We also have official Docker images. Most operating systems also offer BIND 9 packages for their users. These may be built with a different set of defaults than the standard BIND 9 distribution, and some of them add a version number of their own that does not map exactly to the BIND 9 version.
The BIND Administrator Reference Manual (ARM) included in the BIND distribution is the primary reference for BIND configuration. See the Best Practices documents in our Knowledgebase for configuration recommendations.
Resolver users may find Getting started with Recursive Resolvers to be useful. There are a number of excellent books on BIND; Ron Aitchison’s DNS for Rocket Scientists is generously posted on the Internet at Zytrax.com and can be a very helpful online reference tool.
Most users will benefit from joining the bind-users mailing list. We advise all users to subscribe to bind-announce@lists.isc.org to get announcements about new versions and vulnerabilities. For other news, see our BIND blogs.
If your DNS is critical to your business, we recommend you subscribe for technical support from ISC.
The BIND Administrative Reference Manual is the definitive command reference, but there are many other useful technical resources, including our knowledgebase, and the active user mailing list.
Latest Development version BIND ARM, Current Stable version BIND ARM
The ISC ‘KB’ includes both key policies and plans, such as the Software Support Plan as well as detailed technical articles, such as the BIND 9 Signifcant Features Matrix showing which features have recently been added or removed.
ISC technical staff frequently give talks at industry meetings. These can be an interesting source for random news and updates about BIND.
We try post significant oustanding unfixed issues in our BIND wiki here: Known issues in BIND 9.18, Known issues in BIND 9.20,
The BIND team do most of their development work in a publicly-accessible, self-hosted GitLab instance. Anyone may read the issues and code there: to make a comment or add an issue, you must create a (free) account. Please note that we have an aggressive anti-abuse policy, out of necessity.
The bind-users mailing list is a great community resource. Visit the list page to subscribe, or visit the list archives to read older posts. We hope everyone will participate on the list and help other users with patience and courtesy.
The NIST Secure Domain Name System (DNS) Deployment Guide was re-written in 2025. There is some good, solid DNS advice here.
The DNS-OARC working group on Best Current Practices has created this helpful table of existing BCP documents for DNS.
ISC has a well-developed system for handling software vulnerabilities responsibly. Here are some resources to help you secure your deployment.
This policy describes our committment and timeline for handling disclosures. This document explains how we score vulnerabilities, using the CVSS scoring system, to determine their severity.
View the BIND 9 Software Vulnerability Matrix for a listing of all the vulnerabilities that apply to current (not EOL) versions of BIND, or see the table which shows vulnerabilities by software version. Each vulnerability number is linked to the original Advisory document
You might wish to Verify the Integrity of ISC Downloads using PGP / GPG. A few years ago we changed our ISC software signing process.
We recommend all users subscribe to the low-traffic bind-announce mailing list. We announce new version, including those with serious or critical security patches, on this mailing list.
| Service Options | Gold support |  Silver support |
Bronze support | Basic (no support) |
|---|---|---|---|---|
| Critical issue response | 30 minutes, 24x7 | 1 hour, 24x7 | 2 hours, business hours only* | not included |
| Standard issue response | 4 business hours* | 8 business hours* | Next business day | community support via public mailing list |
| Early vulnerability notifications | 5 days | 5 days | 5 days | 3 days |
| Stork support | Available | Available | Available | Community support via user mailing list |
| Purchasing | Quotation/Purchase order | Quotation/Purchase order | Quotation/Purchase order | Quotation/Purchase order |
Pricing based on deployment size and service level.
Contact ISC for a quoteJoin the bind-users mailing list to offer help to or receive advice from other users.
Join NowBefore submitting a bug report, please ensure that you are running a current version. Then, if your issue is NOT a potential vulnerability, please log your report as an issue in our BIND GitLab project. If you think this bug may be a vulnerability, please open a confidential issue in our GitLab instance (preferred) or send an email to bind-security@isc.org.
ReportTest a domain to ensure full reachability and compliance with EDNS standards.
Test| Administrator Reference Manual (ARM) | Links to current ARM on Read The Docs | |
| Binary packages | CentOS & Fedora packages from ISC, Ubuntu package from ISC | Debian -BIND 9 ESV, Debian - BIND 9 Stable, Debian - BIND 9 Development version |
| Software version options | Supported operating systems | ISC’s Software Support Policy and Version Numbering |
| Features and versions | BIND 9 Significant Features Matrix | BIND 9 Changes file |
| Vulnerabilities | ISC Software Defect and Vulnerability Disclosure Policy | BIND 9 Vulnerability Matrix |
| Best practices | Authoritative Systems | Recursive Systems |
| DNSSEC | Additional references | |
| US Government user information | Capability statement and other references | BIND 9 Security Technical Implementation Guidelines |
| Other | DNS tools and resources | History of BIND |