Prepare for more frequent BIND security updates
Plan for more frequent BIND security updates, at least for the remainder of 2026.
Read postEveryone who has and will participate in supporting this initiative should feel they have accomplished something worthwhile. Some operators thought it was unwise that Flag Day was set for a Friday, and were taken by surprise by the level of user concern. Some of the Twitter posts were kind of silly and needlessly alarmist. Characterizing this as a “Flag Day” exaggerated how sudden the real change on the Internet would be, but the effect it had, of providing everyone with a goal date, achieved the objective. The DNS community as a whole did accomplish at least three things over the past year:
We rate-limited the tester to 10 queries per second, to limit its potential as a DDoS tool. We averaged 2-3 tests per second for most of the month! About half of these, or 2312494 tests, were initiated through the www.dnsflagday.net site. This many people testing and validating their DNS implementation, has got to be good for the overall DNS hygiene.
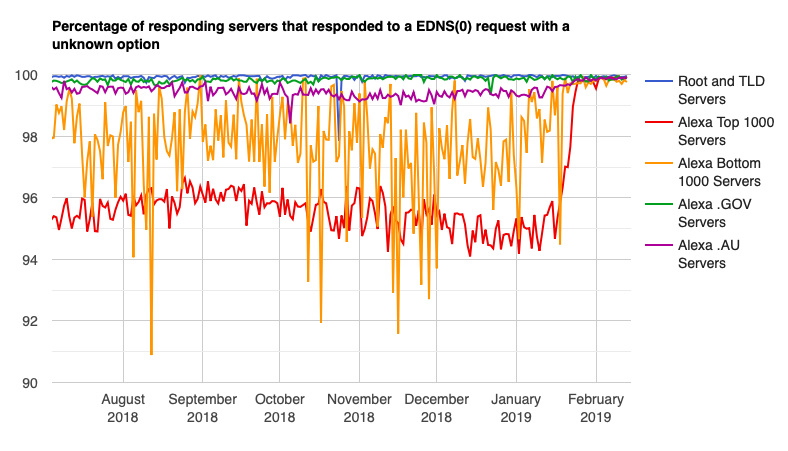
Although we have seen gradual improvement over the past couple of years, that slow rate of improvement accelerated sharply as people saw the Flag Day deadline approaching. The chart below shows the most critical EDNS compatibility issue – servers that would not respond to a query that included an unknown EDNS(0) option. These were the servers that would appear to be unavailable after Flag Day.
This problem is almost always caused by firewalls blocking EDNS, and it was dramatically improved by Flag Day.
We saw significant improvement in the most important compatibility numbers for the Alexa top 1M sites in January. We were already at >96% success on these basic tests at the beginning of 2017, but fixing the last few percentage points was going very slowly. That accelerated sharply in January.
The most wonderful thing was, a few top level domains tested all of their child domains and published reports about their compliance. We know that Switzerland, .ch, downloaded the ednscomp test tool and tested their domains a year or more ago. A few others who also have been working on improving EDNS compliance published compliance reports for Flag Day:
A number of vendors, including firewall vendors and hosted service providers, tested their own products and services and published their status and plans to remedy remaining EDNS compatibility problems.
BlueCat: https://www.bluecatnetworks.com/blog/dns-flag-day-is-coming-and-bluecat-is-ready/
Citrix: https://support.citrix.com/article/CTX241493
DNSimple: https://simpledns.com/news/78/simple-dns-plus-v-8-0-build-108-released-dns-flag-day-update
EfficientIP: http://www.efficientip.com/dns-flag-day-notes/
F5: https://support.f5.com/csp/article/K07808381?sf206085287=1 and https://worldtechit.com/dns-flag-day-for-f5-dns/
InfoBlox: https://community.infoblox.com/t5/Community-Blog/DNS-Flag-Day/ba-p/15843?es_p=8449211
Juniper: https://kb.juniper.net/InfoCenter/index?page=content&id=TSB17513
Microsoft Azure: https://azure.microsoft.com/en-us/updates/azure-dns-flag-day/
Microsoft Windows: https://support.microsoft.com/en-sg/help/4489468/windows-server-domain-name-system-dns-flag-day-compliance
Palo Alto Networks firewall: https://live.paloaltonetworks.com/t5/Community-Blog/DNS-Flag-Day-Are-You-Ready/ba-p/248284
Pulse: https://kb.pulsesecure.net/articles/Pulse_Secure_Article/KB43996
SimpleDNS: https://simpledns.com/news/78/simple-dns-plus-v-8-0-build-108-released-dns-flag-day-update
Dyn: https://dyn.com/blog/what-you-need-to-know-about-dns-flag-day/
Exabytes: https://support.exabytes.com/en/support/discussions/topics/14000013075
Google: https://groups.google.com/forum/#!msg/public-dns-announce/-qaRKDV9InA/CsX-2fJpBAAJ
Quad9: https://quad9.net/dns-flag-day-2019/
Valimail: https://www.valimail.com/blog/what-dns-flag-day/
These are just a few of them:
Carsten Strotmann on Heise.de: https://www.heise.de/newsticker/meldung/DNS-flag-day-Initiative-gegen-veraltete-DNS-Server-und-Middleboxen-4289779.html
Cricket Liu on Tech Target: https://searchsecurity.techtarget.com/answer/Will-DNS-Flag-Day-affect-you-Infobloxs-Cricket-Liu-explains
APNIC: https://blog.apnic.net/2019/01/17/are-you-ready-for-dns-flag-day/
LACTLD: https://lactld.org/en/novedades/interview-hugo-salgado-cl-dns-flag-day.html
Malaysian National Cyber Security: https://www.nacsa.gov.my/announce_dns.php
What's New from ISC